The concept of the Abacus Darknet embodies a fascinating intersection of technology, privacy, and illicit activity. As the darker side of the internet continues to evolve, the Abacus Darknet emerges as a mnemonic that captures the complexity of navigating this hidden realm. In its essence, it highlights the use of sophisticated tools and methods for anonymity while also hinting at the more obscure and questionable practices found within such networks.
This forward-thinking approach has created a platform that stays ahead of both technical threats and law enforcement capabilities. Looking at Abacus's history reveals a pattern of proactive security upgrades rather than reactive responses. The quality standards have increased proportionally, with more vendors having cybersecurity or cryptography backgrounds. Abacus Market implements multiple layers of security to protect user anonymity and transaction privacy. What's particularly impressive is how they've implemented enterprise security practices while maintaining darknet-grade anonymity. Always verify URLs through multiple independent sources and check PGP signatures from market administrators.
Understanding the Darknet
The term "Darknet" refers to parts of the internet that are not indexed by traditional search engines. Accessing the Abacus Darknet typically requires special software, such as Tor, which facilitates anonymous communication and browsing. Users frequent these spaces for various reasons ranging from the pursuit of privacy and freedom of speech to engaging in illegal activities.
Features of the Abacus Darknet
What sets the Abacus Darknet apart from other segments of the Darknet is its focus on leveraging advanced algorithms and data structures reminiscent of an abacus. This theme of calculation and complexity mirrors the multitude of challenges users face when trying to find information or services, particularly in a realm where traditional means of verification are absent.
Activities within the Abacus Darknet
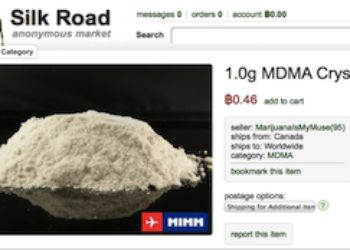
Within the Abacus Darknet, users encounter a wide range of activities. Some turn to these networks to discuss politics freely, while others seek out illicit goods and services. The absence of regulation pushes individuals to develop their own rules and checks to maintain a semblance of order. Despite its reputation, many users are drawn to the underlying theme of information and tools that can support both legal and illegal endeavors.
- Blockchain intelligence firm TRM Labs reports that Abacus shutting down so abruptly has all the indications of either an exit scam or a covert law enforcement operation dismantling the activity.
- Launched in 2020, Archetyp wasn’t just another black market, it was the market.
- They function primarily as black markets, selling or brokering transactions involving drugs, cyber-arms, weapons, counterfeit currency, stolen credit card details, forged documents, unlicensed pharmaceuticals, steroids, and other illicit goods as well as the sale of legal products.
- The Tor Browser is the primary gateway for entering the deep web, including the Abacus darknet.
- What are initial access brokers IABs on the dark web?
The Role of Anonymity

One of the key attractions of the Abacus Darknet is its promise of anonymity. This attribute not only safeguards the identities of users but also emboldens individuals to engage in activities without the fear of repercussions. While this can lead to the proliferation of illegal trade and cybercrime, it also offers a sanctuary for those seeking to escape oppressive regimes or censorship.
Risks and Consequences
However, venturing into the Abacus Darknet comes with significant risks. Users may encounter scams, hacking attempts, and law enforcement operations targeting illegal activities. The ephemeral nature of many services and the potential for betrayal in the form of false advertising or malicious intentions create an environment of uncertainty and danger.
Conclusion
The Abacus Darknet serves as a vivid example of the complexities associated with the hidden facets of the internet. As users navigate its shadowy corridors, they must balance the allure of anonymity and innovation against the ever-present threat of risk and harm. Ultimately, understanding the Abacus Darknet requires a cautious approach, recognizing its dual nature as both a tool for empowerment and a potential vortex of chaos.